







About
Product Details
Included in the iOT 365 Cybersecurity Platform
- Incident Detection System
- Agentless Security Incident and Event Manager (SIEM)
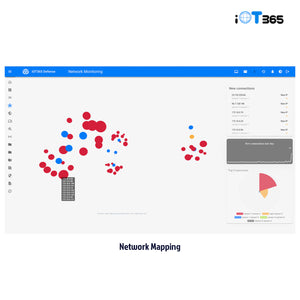
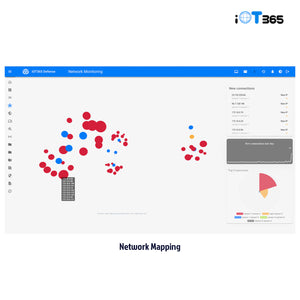
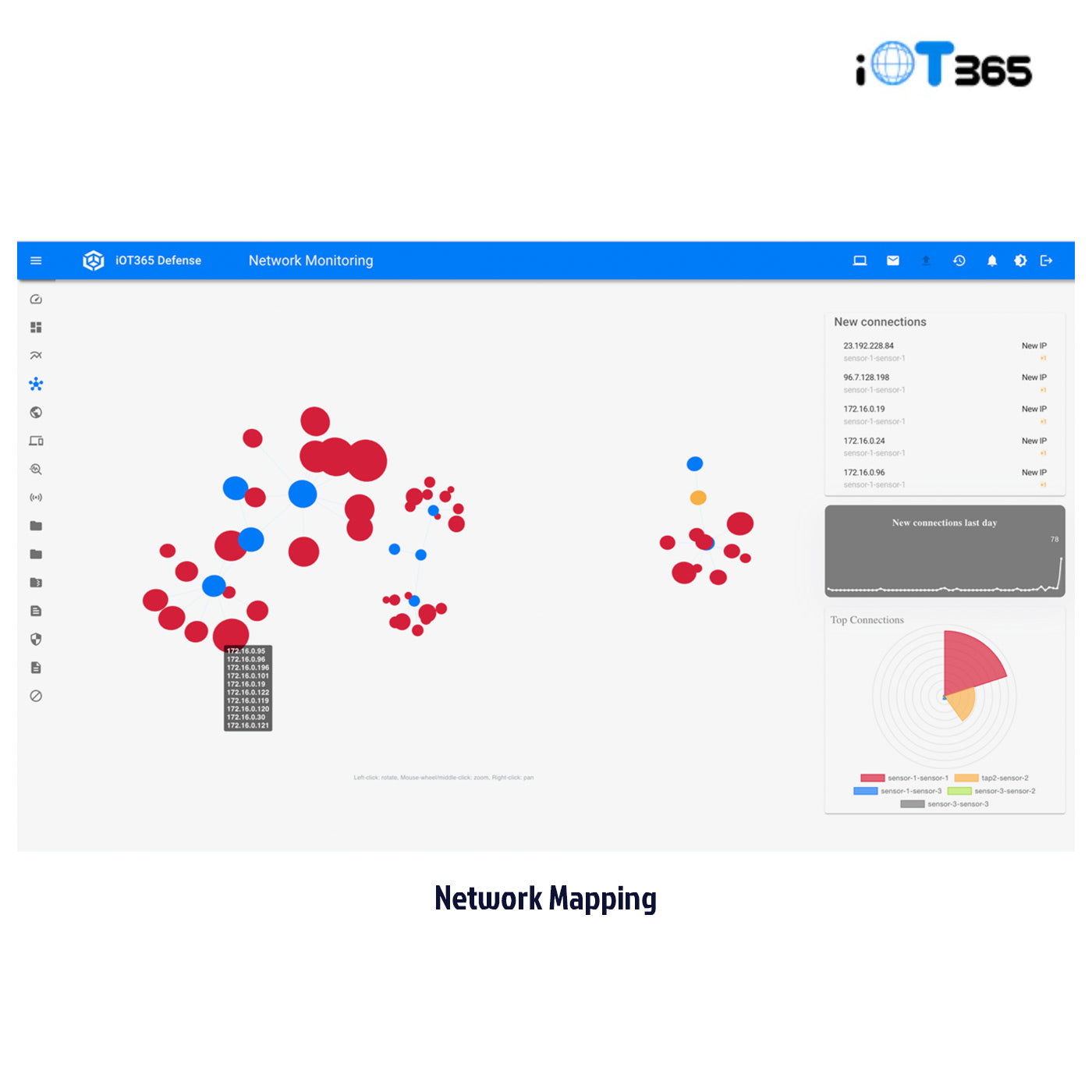
- Network Discovery and Mapping
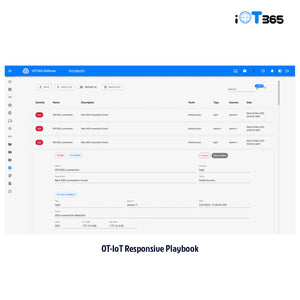
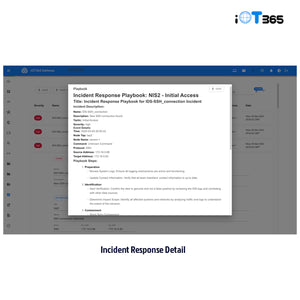
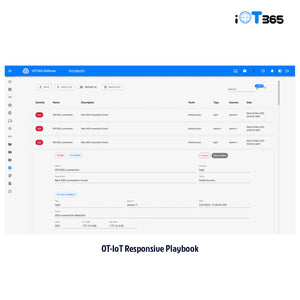
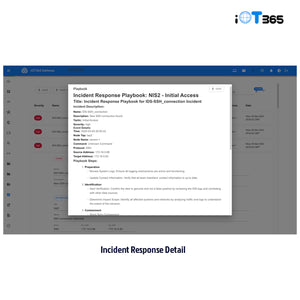
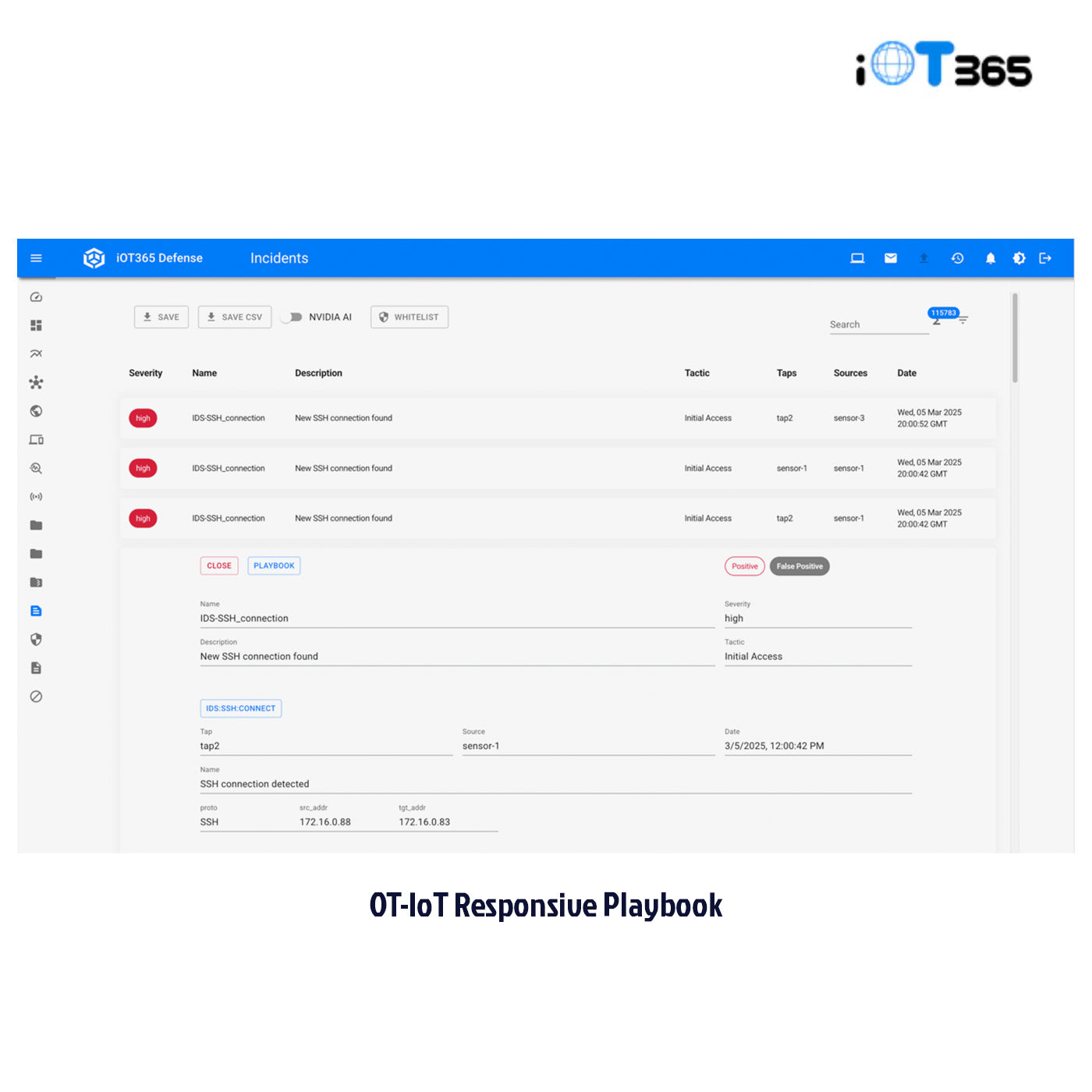
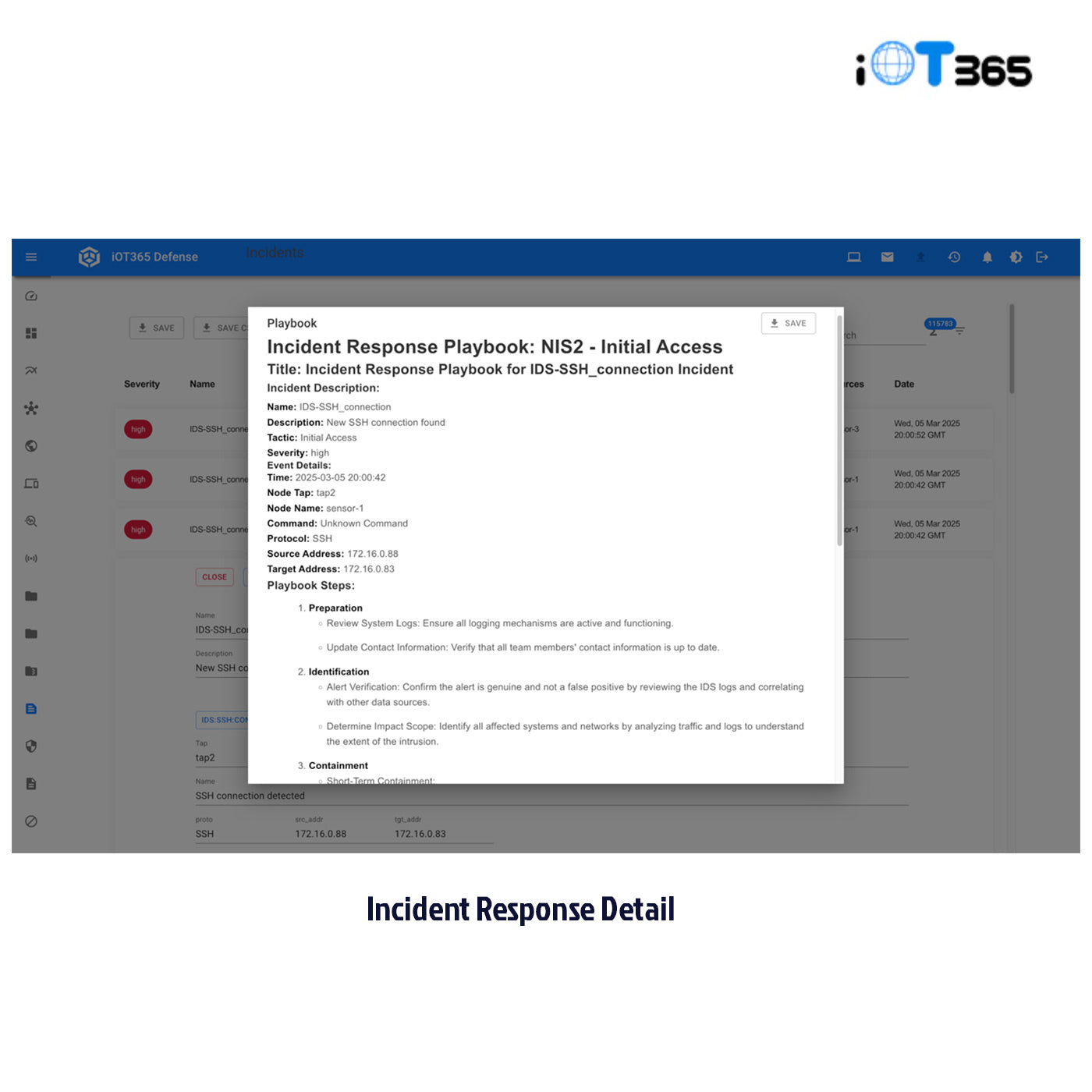
- AI-Generated Response Playbooks
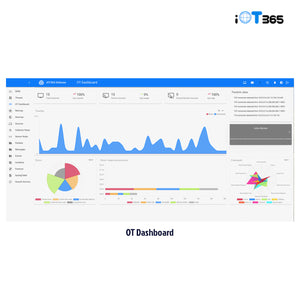
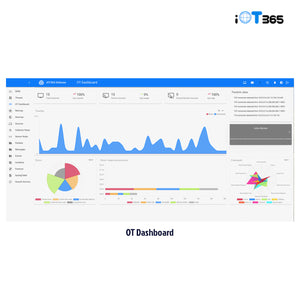
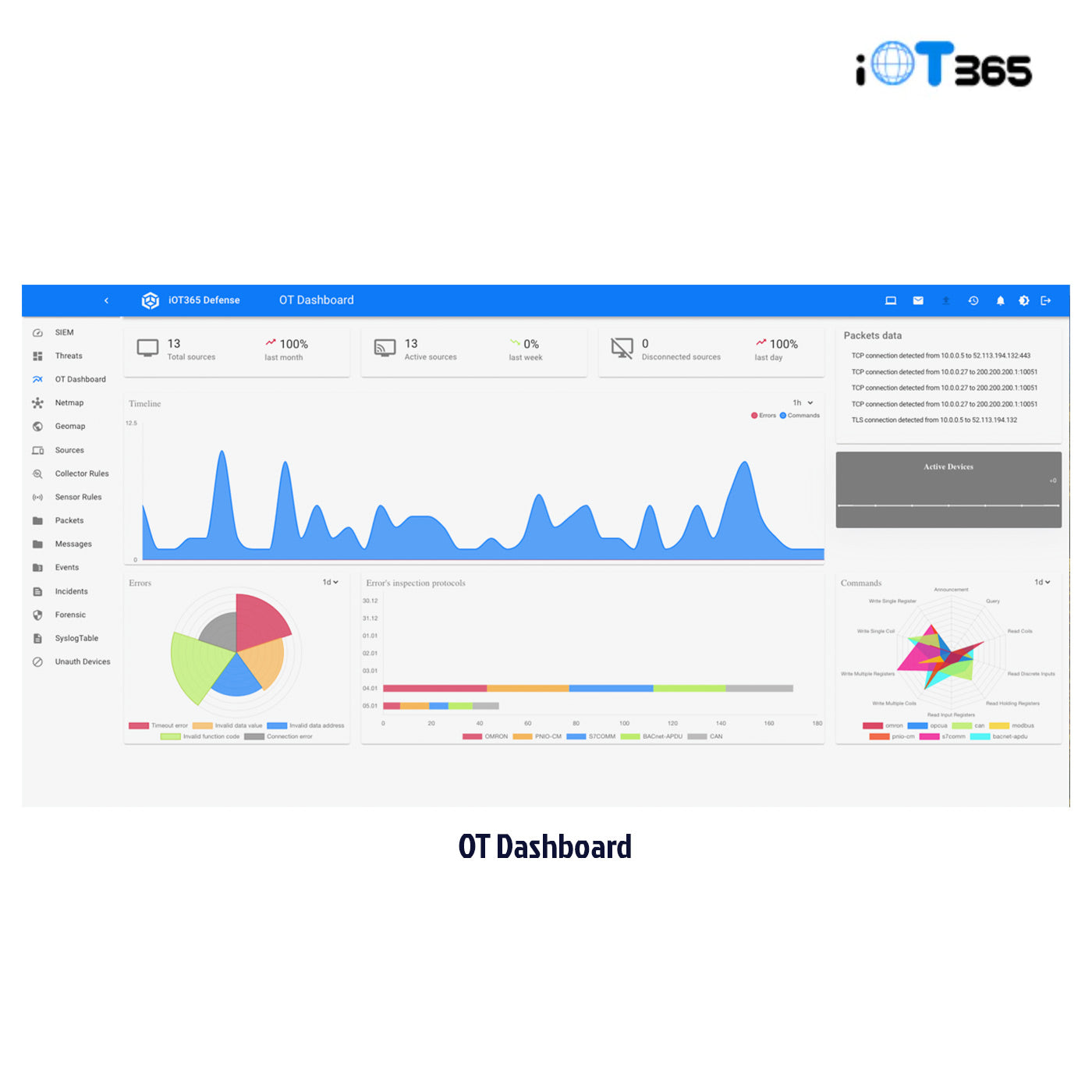
- OT Message Monitoring
- AI False Positive Reduction
- Forensic Tools
- Support for the Widest Range of OT and IoT Network Protocols
- Smart Collectors (virtual collectors optional)
- Vulnerability Assessment (optional module)
- OT/IoT Security Operations Center (SOC) (optional module)
- IoT Data Monitoring (optional module)
Advanced Cybersecurity for Your OT and IoT Devices
In today’s interconnected world, every new IoT and OT device on your network creates a potential entry point for cybercriminals. The growth in industrial automation and the explosion of IoT devices have made OT and IoT devices prime targets for cyberattacks.
Traditional IT cybersecurity platforms fall short in protecting OT and IoT devices, and the first generation of OT and IoT cybersecurity platforms have been too complex, too costly, and incomplete solutions at best. That’s where iOT365 comes in.
The all-in-one AI-powered OT/IoT cybersecurity solution
The iOT365 Cybersecurity AI Cybersecurity platform provides you with a complete solution for detecting, analyzing and remediating cybersecurity threats to your OT and IoT devices and networks.
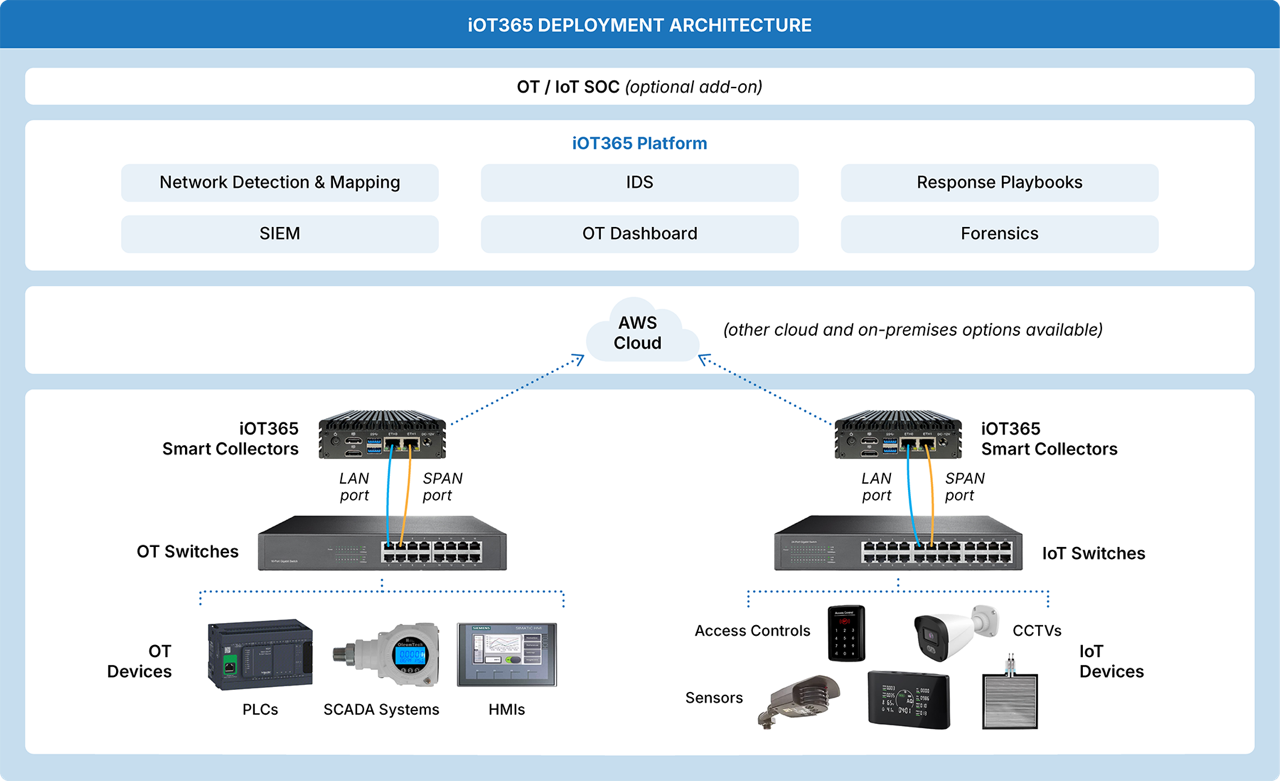
The platform’s compact and lightweight Smart Collectors easily connect to your OT and IoT switches and process, encrypt and transmit a copy of all of your network traffic to the iOT365 cloud software.
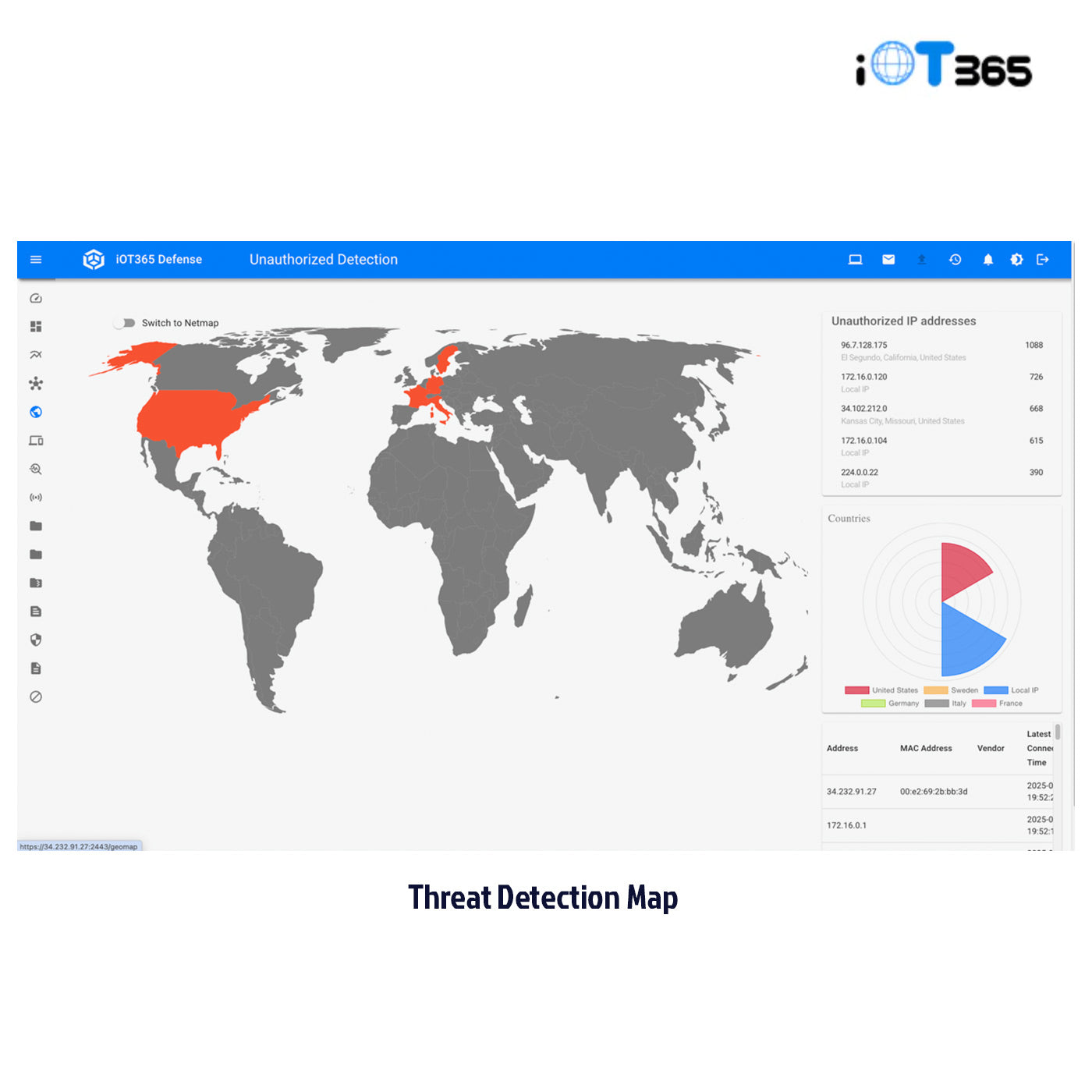
Within about 15 minutes after you’ve deployed the Smart Collectors, the platform will discover and map your entire OT and IoT network, immediately detect potentially threatening device connections.
Real-time visibility on cyber threats and how to handle them.
From that point, each packet running through your switches is analyzed through multiple layers of AI to identify events and which of them are true cybersecurity incidents. For each incident, the platform generates alerts to your team and provides a detailed AI-generated response playbook on how to contain and then remediate the threat.
Additional platform features include forensic tools, an OT dashboard which can give you early visibility to problems with your OT devices, and threat analysis. Optional add-ons include vulnerability assessments, iOT data dashboards, and a full OT/IoT security operations center (SOC).
Who Should Deploy This Technology?
What Other Options Should Be Considered When Deploying This Technology?
Frequently Asked Questions (FAQ):
Typical Deployment of the iOT 365 Cybersecurity Platform
Included in the iOT 365 Cybersecurity Platform
- Incident Detection System
- Agentless Security Incident and Event Manager (SIEM)
- Network Discovery and Mapping
- AI-Generated Response Playbooks
- OT Message Monitoring
- AI False Positive Reduction
- Forensic Tools
- Support for the Widest Range of OT and IoT Network Protocols
- Smart Collectors (virtual collectors optional)
- Vulnerability Assessment (optional module)
- OT/IoT Security Operations Center (SOC) (optional module)
- IoT Data Monitoring (optional module)
Advanced Cybersecurity for Your OT and IoT Devices
In today’s interconnected world, every new IoT and OT device on your network creates a potential entry point for cybercriminals. The growth in industrial automation and the explosion of IoT devices have made OT and IoT devices prime targets for cyberattacks.
Traditional IT cybersecurity platforms fall short in protecting OT and IoT devices, and the first generation of OT and IoT cybersecurity platforms have been too complex, too costly, and incomplete solutions at best. That’s where iOT365 comes in.
The all-in-one AI-powered OT/IoT cybersecurity solution
The iOT365 Cybersecurity AI Cybersecurity platform provides you with a complete solution for detecting, analyzing and remediating cybersecurity threats to your OT and IoT devices and networks.
The platform’s compact and lightweight Smart Collectors easily connect to your OT and IoT switches and process, encrypt and transmit a copy of all of your network traffic to the iOT365 cloud software.
Within about 15 minutes after you’ve deployed the Smart Collectors, the platform will discover and map your entire OT and IoT network, immediately detect potentially threatening device connections.
Real-time visibility on cyber threats and how to handle them.
From that point, each packet running through your switches is analyzed through multiple layers of AI to identify events and which of them are true cybersecurity incidents. For each incident, the platform generates alerts to your team and provides a detailed AI-generated response playbook on how to contain and then remediate the threat.
Additional platform features include forensic tools, an OT dashboard which can give you early visibility to problems with your OT devices, and threat analysis. Optional add-ons include vulnerability assessments, iOT data dashboards, and a full OT/IoT security operations center (SOC).

Translation missing: en.products.product.sku:
iOT365 AI Cybersecurity Platform
- Regular price
- $9,995.00
- Sale price
- $9,995.00
- Regular price
-
Couldn't load pickup availability
Popup Title
Popup Title
Product Specs
Don't see what you're looking for?
Give us a call at (508) 289-1195



Resources for iOT365 AI Cybersecurity Platform

















